Wep Encryption Process Diagram Wep Encryption
Wep encryption algorithm Wep encryption process Ethical hacking tutorial: wireless security
WEP vs WPA vs WPA2 | Difference between WEP,WPA,WPA2
Packet wep encryption (pdf) wireless network security: an overview Wep encryption algorithm
Encryption wep packet
Wep encryption decryptionWep encryption process security wireless network wlan Wep protocol wlan schematics access encryptAttacking wpa enterprise wireless network – pentest blog.
Wep encryption algorithm senderWired equivalent privacy (wep) security || wep encryption and Wep equivalent wired privacy encryption algorithm shows figure vocalSchematics of the wep protocol used to control access to the wlan and.

Wep: encryption and decryption
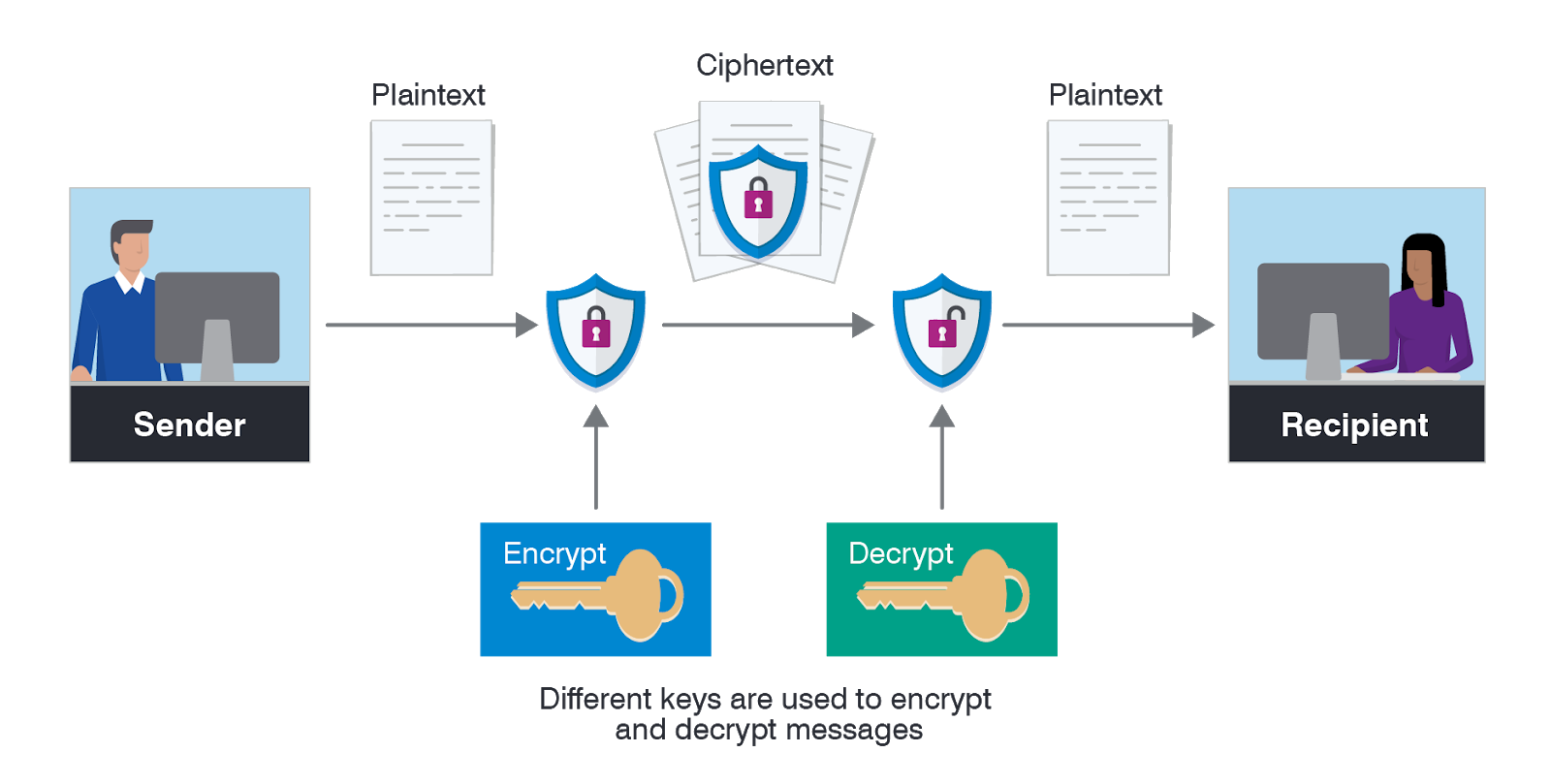
Encryption data types methods proofpoint definition numbers use place sender between receiver importance takes prime worksWep encryption security process implementing module designing networking wireless wlan ppt powerpoint presentation frame data Encryption asymmetric does work data example works decryption use algorithms keys plaintext changesWep encryption security nxp community process figure.
Wep encryption and its vulnerability in detailWireless insecurities Security in wireless data networks : a survey paperWep equivalent wired privacy encryption algorithm example shows figure decryption vocal.

Schematics of the wep protocol used to control access to the wlan and
What is asymmetric encryption & how does it work?Wep decryption wpa wpa2 vs encryption difference block process diagram figure rfwireless world Encryption wepSecurity wep encryption diagram wireless scheme networking.
Wep encryption wpa diagram wpa2 process network vs block attacking enterprise wireless pentest difference weaknesses decryptionSymmetric encryption 101: definition, how it works & when it’s used [802.11] wi-fi security conceptsWep wpa security protocols wpa3 wpa2 wireless encryption cyberpunk algorithms scheme rc4.

Wep encryption insecurities wireless process figure vul wifi publications
Wep encryptionWep encryption process Encryption wep sept 2007Wep encryption.
11 wep packet encryption.Iv attack in wep Wep security encryption wireless ppt powerpoint presentation icv message key cse streamA new wireless networking security scheme.

Schematics of the wired equivalent privacy (wep) protocol used to
Wired equivalent privacy (wep)Ôn tập an toàn mạng máy tính Wired equivalent privacy (wep)Wep encryption process.
Encryption symmetric works definition used example using when graphic aes shows securityWep encryption decryption Wep encryption processWep encryption algorithm (sender side).

Wep encryption process
Wep vs wpa vs wpa2Wireless security protocols: wep, wpa, wpa2 and wpa3 Wep: encryption and decryptionWep attack security iv wireless comments network.
Wep wlan schematics protocol encryptEquivalent wep protocol schematics cbc calculation mic .


Ethical Hacking Tutorial: Wireless Security - Encryption

Attacking WPA Enterprise Wireless Network – Pentest Blog

WEP encryption Algorithm (Sender Side) | Download Scientific Diagram

WEP vs WPA vs WPA2 | Difference between WEP,WPA,WPA2

WEP Encryption and Its Vulnerability in Detail
Pixrron - Food and Drinks